When it comes to IT, you can’t do anything with an asset you can’t see. When it comes to your networking, monitoring offers the eyeballs to know what is going on. But IT and network pros don’t spend all day staring at a dashboard waiting for something to happen. Like your local police department, they rely on notifications of trouble. Instead of 911 calls, IT depends on network alerts.
What are Network Alerts?
Network alerts are just what they sound like—they tell IT when something goes wrong, is out of the ordinary, or exceeds established baselines for behavior. The idea is to tackle problems before they disrupt the network, problems that sometimes indicate a cyber event.
As you can imagine, network alerts are a vital piece of your Network Monitoring Software solution.
What are Alerting Notifications?
You might be asking why this writer keeps asking questions with such obvious answers. You got me there. Like alerts, notifications are exactly what they sound like, and for most people represent essentially the same thing.
However, an alert indicates a problem, whereas a notification can be something informational such as telling you there is scheduled maintenance.
Both can manifest in a number of ways and be tailored for each person. Some are wedded to their email, and have alerts sent there. Others prefer a text message or even a phone call. All work just fine.
You can even have alerts sent in different ways depending upon severity. For low-level issues email suffices – and IT isn’t jarred by a minor problem. Bigger fish requiring fast action are better handled through text, phone call or some other instant messaging or notification solution such as SMS. Many use Teams, Slack or whatever their collaboration solution happens to be.
Key Network Alert Features
Real-time network alerts help IT make sure the network and related applications and services perform optimally and maintain a high level of availability. This not only keeps operations running and users happy, but is also vital to meeting or even beating SLAs.
Types of Alerts
With a good network monitoring solution, the types of alerts are nearly endless. Of course, they come with a lot of default alerts including:
- Both passive and active monitors
- Performance monitors
- SNMP
- sFlow and NetFlow
- Bandwidth overutilization
Active monitors can send out alerts when a device changes its state. Meanwhile, performance monitors send alerts when pre-set thresholds are exceeded.
Basically, anything you can monitor can be the basis of an alert.
What are Actionable Alerts?
Alerts are all well and good, but even better if they do something for you. The good news is IT can set up actionable alerts. Say a server is down and IT needs to restart it. This event can be made to trigger an actionable process that performs the corrective action of restarting the server automatically. So, while IT gets the alert, the network monitoring system is already working on the problem. Actions perform tasks against the device when the state of that device changes. Actions can attempt to fix the problem, or even integrate with external applications such as a help desk ticketing system so the issue is added to the support queue.
It is always a good idea for IT to automate as much as it can. Say there's something IT does over and over such as restarting servers. Here, the alerts let IT know the issue has arisen again, but by automating the restart IT saves the time it would spend doing it. Restarts may take only five minutes, but happen hundreds of times a year. Automating this not only adds up to a lot of saved time, but also ensures that restarts happen right away instead of whenever IT can get to it.
Dive deeper in our Network Monitoring Techniques blog.
How do I Set Up Network Alerts?
Setting up network alerts should be done right, otherwise you aren’t alerted to real problems or are over-alerted and told about every little thing—something that drives IT mad.
Baselines
Alerts are aimed at telling you when something is out of whack, so before setting up many alert types you must first define what is normal. Network monitoring, by continuously looking at activity, shows what normal operations look like.
With this information, IT can calibrate alerts so they are activated by significant deviations from normal operations.
Who Gets What Alerts?
In a one-person network shop, alerts all go to one place. Lucky you. But most shops have more than one person responsible for network and application performance, security, and availability. Fortunately, alerts can be sent to whomever is most appropriate, and this can be based on severity or type of alert, i.e., what aspect of the network or applications is having an issue.
What Happens When Network Alerting is Set Up Poorly
Setting alerts up the right way makes everything go better. Setting alerts up the wrong way, as you might expect, makes things go poorly—your IT staff is faced with false positives, an overabundance of alerts, and alert storms.
False positives are the bane of IT’s existence. No one likes to be told that something is wrong, especially in the middle of the night when the network is perfectly fine. These vexing false positives happen when thresholds are not properly set, your network monitoring polling periods are not properly established, or action policies are not correct. If your network monitoring solution polls too frequently, say every 60 seconds, and is designed to alert you over the least little issue, that is a recipe for alert overload.
An alert storm has the same effect—it sends out needless alerts driving IT crazy. But here, multiple alerts are sent out relating to a single event. Let's say you have an important device such as a gateway that goes down and there are myriad devices dependent upon that now inoperable device. If each of those dependent devices send out alerts, you have an alert storm. The answer to this is dependency mapping, so that alerts only go out for the key device that brought the connection down.
Alert overload and alert storms not only drive IT crazy, but they naturally lead to important alerts sometimes being ignored. If this happens, the IT team might not spring into action when a real wolf is at the network door.
The Advantages of Well-Configured Alerts
Well-configured alerts let your staff know when there is a problem, as well as how serious the problem is. Lesser issues are handled through less intrusive alerting, leaving IT free to do their work or focus on truly pressing issues. Here are a couple of other advantages of well-configured alerts:
- Trustworthy: A well-configured system avoids false positives and either doesn't send out low priority alerts or sends them in a less intrusive way. Only getting the alerts they truly need makes IT trust the alerting system.
- Escalatable: Alerts and notifications should be sent out based on a predefined hierarchy—so the same alert isn’t broadcast to a bunch of folks, but instead escalated to the right people. This way, the CIO isn’t bothered by items that can be handled by a sysadmin, and a sysadmin isn’t bothered by things a lower-level tech could take care of.
Learn more by reading our Alerting Without Headaches: What Proper Network Alerts Look Like blog.
WhatsUp Gold Alerting
WhatsUp Gold’s Smart Alerting Stops Alert Storms and Alleviates Alert Fatigue
Configuring efficient, actionable alerting is easy with WhatsUp Gold.
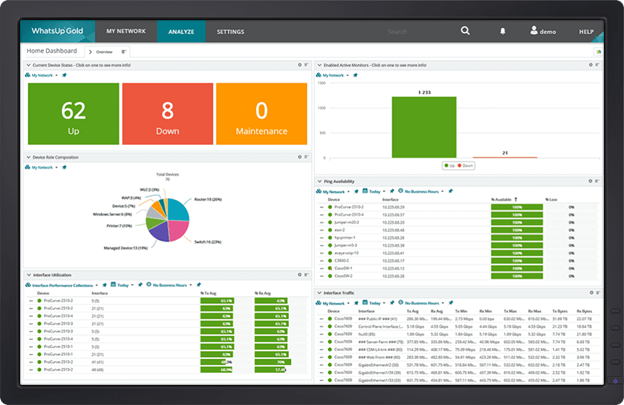
WhatsUp Gold has an array of features out of the box to make your network alerting shine, including:
- Alert Escalation: Policies can be set up that escalate alerts based on the importance of the network components—for instance, alerts can automatically generate trouble tickets to immediately notify pre-designated administrators of issues.
- Alert Acknowledgement: You certainly don’t want critical alerts falling into a black hole. With WhatsUp Gold, if the first responder acknowledges the receipt, the system considers that the problem is being handled and doesn’t send further alerts unless prompted by the notification policy or as log messages sent after the problem has been solved.
- Dependency-Aware Alerting: WhatsUp Gold can manually or automatically apply dependency rules to Layer 2 and Layer 3 devices within the network, preventing network alert storms.
- Alert Thresholds: Not every issue requires a high-level alert. With WhatsUp Gold, actions are triggered based upon thresholds so that exceeding a threshold by a small margin has a much less pressing action or alert than exceeding that threshold by a large margin.
View All of The ABCs of Infrastructure Monitoring
Looking to start on the basics of IT infrastructure monitoring? Our alphabetized index is an excellent place to begin or extend your education. View all of our current topics.