Over the past week, news broke about a rogue device that had gone unnoticed on NASA’s Jet Propulsion Lab (JPL) IT network. The fact that a Raspberry Pi went unnoticed for almost 10 months is a clear signal of network management issues and lackluster security policies in place within NASA, and other government agencies for that matter.
What is really telling here is that NASA (at least as it pertains to JPL in California) did not have some fairly ordinary security controls and tools in place to notice this device quickly. Ten months in the IT world is a ridiculously long time for something to go unnoticed on a network. From what investigators can tell so far, an employee at NASA had installed the device on the network, but NASA hasn’t yet determined if it’s an inside job. In other words, it is not certain yet if the employee who installed the device did it maliciously.
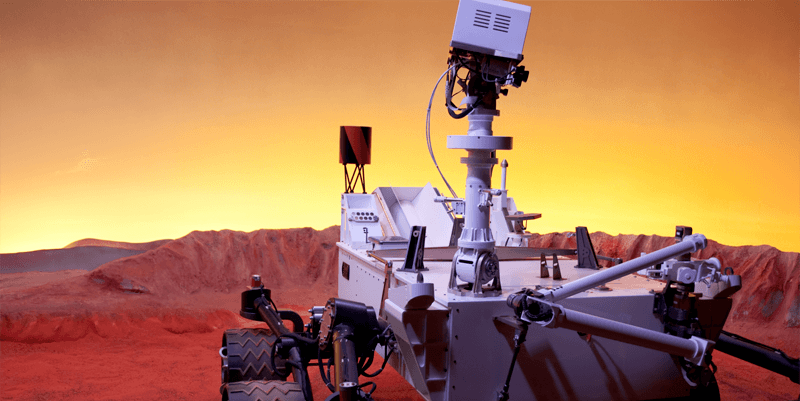
The Raspberry Pi ultimately was used to access data via a gateway that allows external contractors, partners, and foreign space agencies remote access to mission data. One of these missions includes the Mars rover, Curiosity. Although this type of advanced persistent threat (APT) does fall in line with similar attacks in the past by nation-state actors, we still don’t know who the attacker is and no one has yet to be charged with a crime. As with most stories like these, time will tell.
As troubling as it is to hear that NASA was hacked in such a way, it is a fairly easy fix to help avoid issues like this in the future. NASA will need to reassess their security controls on their IT systems and at the very least set up a network discovery tool that can notify system administrators when unwanted devices are hooked up to the network. This type of functionality is at the core of all network monitoring solutions.
Besides preventing end users from connecting unsecured devices to a network, running a network discovery with a network monitoring tool, such as WhatsUp Gold, is the most prudent way to notice if something like a Raspberry Pi is accessing half a gig of data. Most IT teams should be running a network discovery at least once per month if not more. A network discovery is any process that can identify all devices on a network via SNMP, WMI, and/or pinging the devices.
Security should be one of the top concerns of any IT team and that means knowing what’s accessing your network and why. If you don’t know what’s connected to your network you aren’t going to be able to identify unsecured devices like a rogue Raspberry Pi. Shadow IT will always be an issue with end users, training only goes so far, and the dynamics of business networks today make noticing a single rogue device all the more challenging. The fact of the matter is that in this day and age devices are being connected and disconnected all the time.
WhatsUp Gold’s discovery process generates a complete inventory of all networked devices including device type, vendor, serial number, firmware and hardware rev, and the modules installed on the devices. Customers often use this feature to fulfill inventory audits with automatically generated reports on the software installed on servers or network devices.
The lesson learned here is that all IT teams need to be scanning their network regularly using a network monitoring tool.