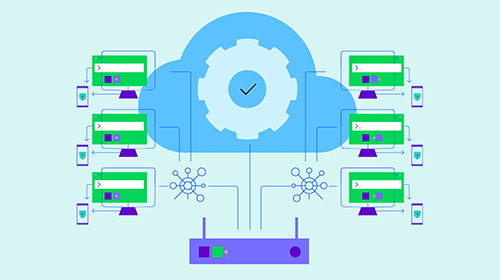
What is Network Traffic Analysis?
Network traffic analysis is a process utilized to monitor incoming network traffic for overall performance, security and assorted maintenance issues. Learn more about the ins and outs of network traffic analysis (NTA), the benefits and more.