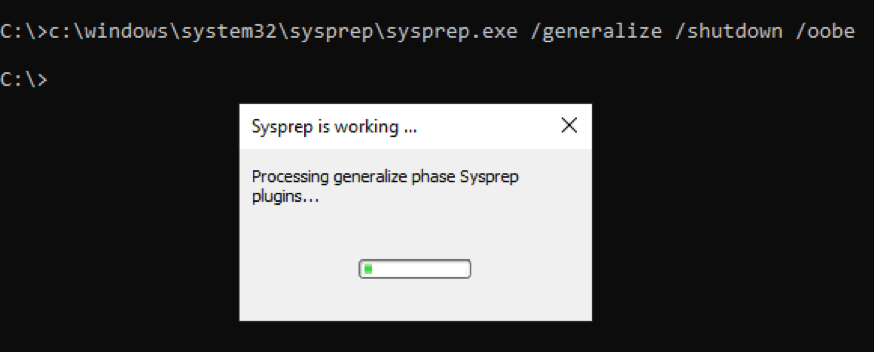
How to Find All Processes Running Under Administrative Privileges with PowerShell
You can get a leg up on a potential attacker by figuring out what processes are running under an administrative account in your organization. One way to do that for absolutely free is to use PowerShell!