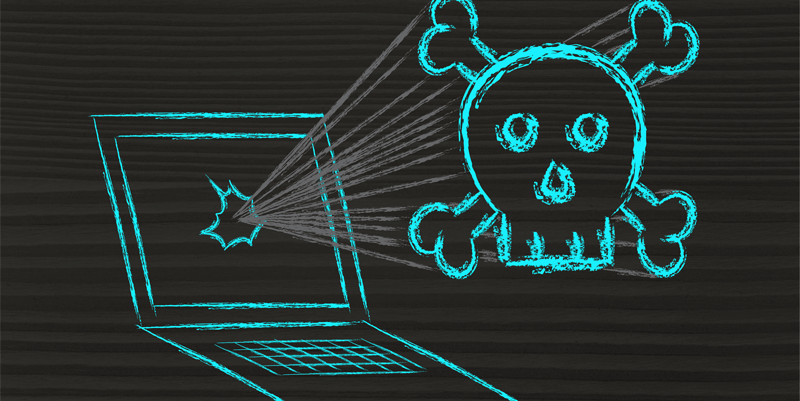
Why Azure Up/Down Monitoring Is So Important
It’s 2:00 a.m. in the United States: Can your employees and customers in Europe and Asia access the applications running in your Microsoft Azure cloud? If you’re not sure on a 24x7 basis what the status is of your Azure servers and applications, it’s time to invest in a third-party monitoring tool.